
As the Federal Bureau of Investigations continues its manhunt on Americans who protested the stolen election at the nation’s Capital in January, the bureau ramped up its assault on the First Amendment by targeting journalists in pre-dawn, knock-the-door-down raids and unconstitutional threats of jail time.
Muckrakers and activists who effectively expose government malfeasance and fail to use secure messaging tools or may find themselves directly in the federal government’s wrath as the Biden Justice Department chills dissent and prosecutes political dissidents.
To protect private data and secure the integrity of private communication, billions around the globe now use services encrypted messaging services like Signal, Telegram and WhatsApp, platforms that are sold to the public under the guise of “securing privacy.”
People feel more confident that what they discuss on these service providers remains secure. Meanwhile, the FBI has the ability to legally access vast amounts of data from the popular “encrypted” messaging accounts of those subject to its probes.
According to the bureau’s internal guide on surveillance titled “Lawful Access,” law enforcement relies more on Facebook’s WhatsApp and Apple’s iMessage to surveil its targets than any other messaging apps in the tech domain.
Despite Facebook CEO Mark Zuckerberg’s insistence that his encrypted messaging service was built around a “privacy-focused vision,” WhatsApp provides law enforcement officials with more real-time information about a user and their activities than nearly any other major messaging tool.
With a subpoena, the bureau can only legally access its target’s basic subscriber information on WhatsApp. With a search warrant, however, law enforcement agencies can legally use WhatsApp to access its target’s address book contacts and the contacts of other WhatsApp users associated with the targeted individual.
While law enforcement cannot legally obtain message content from WhatsApp, the metadata allows law enforcement to identify which users communicate with one another, how often they correspond and a list of every user in their address book – a security breach that could devastate a whistleblower or reporter with confidential sources.
A “pen register” surveillance tracks the specific source and destination of each message sent and received from a targeted individual. In response to a pen register, WhatsApp provides the feds exceptional, nearly real-time surveillance of its target, producing and sending metadata to law enforcement agencies every 15 minutes.
“Return data provided by the companies listed below, with the exception of WhatsApp, are actually logs of latent data that are provided to law enforcement in a non-real-time manner and may impact investigations due to delivery delays,” the FBI guidance states.
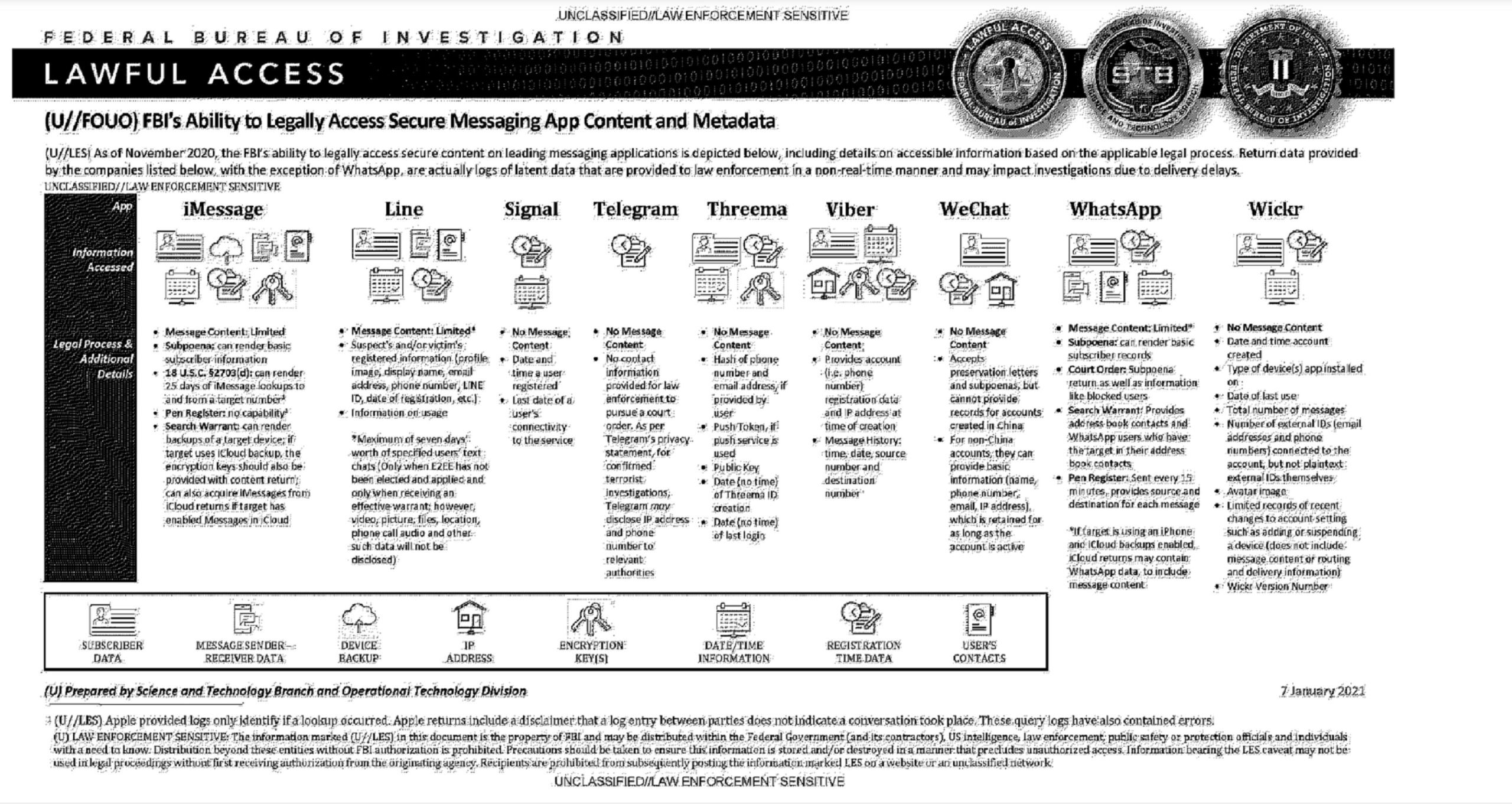
On the other hand, the content of messages exchanged on Apple’s iMessage text service, which is used by 1.3 billion people worldwide, is easily obtainable by the FBI.
Apple turns over swaths of data from the phones of targets to law enforcement from its iMessaging text service, the default service on iPhones. With a subpoena, Apple hands over basic subscriber information of the target and a 25-day backlog of correspondence exchanged on iMessage. Apple also provides law enforcement with a list of people who searched for its target on its iMessage app.
A target who communicates on an iPhone or an Apple product backs up their iMessage activity to an iCloud, law enforcement is able to request back-ups of the surveilled device and access the content sent and received in messages.
To make matters worse, the process in which the FBI and National Security Agency obtain search warrants is ripe for abuse. Big brother gets nearly unanimous approval from the Foreign Intelligence Surveillance Court court to surveil its targets.
The FBI relies on the FISC for approval of wiretaps, data collection, and government requests that allow the agency to monitor suspected terrorists, spies and American citizens and the court approves more than 99 percent of the domestic electronic surveillance requests the deep state brings to its vaulted door.
A 2016 Justice Department report shows the FBI and the National Security Agency made 1,457 requests for permission to the FISA court to conduct electronic surveillance in 2015 and just one application was rejected by the government in all of 2015.
The FISA court also issues “national security letter” subpoenas used by intelligence agencies to compel private companies to turn over personal data on customers.
“These subpoenas contain everything from Americans’ billing information to their browsing histories,” World Net Daily reports. “In most cases, ‘national security letters’ are accompanied by gag orders, legally forcing companies to give up customer data and prohibiting the companies from telling anyone about the process.”
In 2016, the weaponized intelligence agencies illegally obtained FISA warrants to surveil Trump campaign operatives and smeared the president with lies surrounding alleged Russian collusion.
After targeting President Trump throughout his presidency, the FBI began abusing the FISA system in January by raiding and arresting Americans, who witnessed electoral theft in real-time, for protesting the stolen 2020 election.
Now, as the Justice Department takes aim at journalists and media, even the far-left American Civil Liberties Union and mainstream media journalists are rebuking the dangerous precedent set by the federal government infringement on free speech.
The left-wing troll site Rolling Stone first reported on the FBI’s “Lawful Access” guidance on Monday after receiving the document from the Property of the People. Property of the People, an anti-Trump non-profit organization, obtained the Jan. 7 document via a Freedom of Information Act request.
“Privacy is essential to democracy,” Property of the People’s executive director Ryan Shapiro told Rolling Stone. “The ease with which the FBI surveils our online data, mining the intimate details of our daily lives, threatens us all and paves the way for authoritarian rule.”
